1
What is IT incident management?
Imagine you’re in the middle of a critical project, and suddenly, your system crashes. Or perhaps it’s the middle of the night, and your server goes down, affecting countless users. While you can’t avoid all IT incidents, how you handle them can significantly reduce their impact.
You know that proper IT incident management is critical — and that incidents can become costly. On average, organizations lose $14,056 per minute of unplanned downtime — that number jumps to $23,750 per minute for large enterprises. Service interruptions can also damage customer experience and business productivity.
IT incident management is the process of identifying, analyzing, and fixing incidents to restore normal service operations. The goal is to minimize business impact, increase productivity, and prevent business-threatening situations.
2
What is incident management in IT?
Incident management operates as a component of the IT service management (ITSM) framework, focusing on addressing and resolving IT-related incidents.
An IT incident is any unplanned interruption or degradation of IT services. ITOps teams handle various incidents, such as software or hardware failures, email issues, security breaches, user mistakes, or — in a worst-case scenario— outages. Incidents are not to be confused with IT events or problems.
- An incident is any non-scheduled IT service disruption or degradation.
- An event is any observable occurrence in an IT system, whether normal operation or error.
- A problem is the underlying root cause of one or multiple incidents, often hinting at a deeper issue in the IT infrastructure.
According to ITIL guidelines, problem management focuses on preventing or reducing incidents, while incident management addresses real-time issue resolution.
3
Why is optimizing incident management important?
Efficient issue resolution is essential to minimize downtime, preserve reputation, and reduce costs. Incident management is vital for your ability to uphold service-level agreements (SLAs), meet compliance requirements, and efficiently manage risk. Through continuous improvement, your approach can enhance IT system resilience and improve overall business stability.
4
What is the goal of incident management?
If you’re not well-equipped to handle IT incidents, you risk costly outages and unhappy customers. Many organizations still rely on manual incident-management procedures. As a result, they struggle to keep pace with rapidly evolving agile methodologies or hybrid-cloud environments.
Contemporary organizations maintain an incident management team to address unforeseen disruptions and malfunctions. Dependable teams and transparent processes are crucial to manage unplanned incidents and uphold SLAs effectively.
A well-defined strategy plays a pivotal role in prompt and efficient incident resolution. It also helps avert future incidents, refine business operations, and enhance customer satisfaction.
5
Incident management in ITIL
Incident management is a significant component of ITIL service support. ITIL incident management provides the framework for minimizing the negative impacts by restoring services as soon as possible.
Successful ITIL incident management necessitates clear roles among stakeholders. The incident manager oversees the process and ensures timely resolution per the SLAs.
Support levels may cover a range of responses and teams, including:
- The service desk or NOC for initial contact and basic troubleshooting
- Technical teams equipped for quick response using incident-management tools
- Hardware/software engineering teams to address specific system issues
6
What are the five steps of IT incident management?
The ITIL incident management process includes procedures and actions for responding to and resolving incidents.
The process involves five steps. The steps outline the entire incident lifecycle and identify concerned stakeholders, how to detect incidents and convey information to the IT team, and the tools used for resolution.
These are crucial steps in determining and addressing all the aspects of an incident.
Step 1: Incident identification
Detection starts with user alerts, infrastructure metrics, or unusual behavior. Regardless of incident origin, the service desk team logs alerts, noting key details and assigning a unique ID for tracking.
Incident intelligence tools detect and highlight anomalies, ensuring quick responses and fewer escalations. Effective tools can significantly reduce resolution time and streamline incident logs.
Step 2: Incident categorization
Incident response begins after triaging according to your organization’s protocols. Proper triage prevents misclassification. Incidents are grouped for easier tracking and addressing user impacts. After categorization, it’s essential to reference past incidents for insights.
Categorization streamlines information gathering and diagnosis, enhancing incident management efficiency. Until the incident is resolved, these categories guide escalation activity. Successful escalation hinges on accurate categorization and clear responsibilities. Having the right tools ensures effective categorization and transparent escalation.
Step 3: Incident prioritization
Use priority matrices to assess incidents according to importance. The prioritization assists service-desk analysts in gauging response urgency and establishing customer expectations. The system system assigns a prioritization code based on business impact and response urgency when it logs an incident.
Factors that affect prioritization may include:
- Number of affected customers or users
- Number of services or IT systems affected
- Significance of the disrupted service(s)
- Potential revenue loss or resolution cost
Urgency relates to resolution time, SLA targets, and the criticality of the service. Efficient triage requires context, which can be challenging without enough information or system visibility. Incident intelligence tools automate triage, prioritizing to streamline resolution and keep stakeholders informed.
Step 4: Incident response
Incident response uses a structured approach to guide teams through resolution. Following prioritization, the focus moves to containment to prevent further damage.
If unresolved, the issue is escalated for deeper analysis. Key steps include gathering and analyzing data and performing a root-cause analysis (RCA) to pinpoint the incident’s origin, aiming to reduce the mean time to resolution (MTTR).
Be sure to document your incident solution and the probable root cause in your knowledge base or configuration management database (CMDB). You can associate incident records with their relevant CIs in your CMDB, helping teams track incidents — and the assets they impact — over time. Incident response plans must remain dynamic, receiving regular updates and integrating real-time user feedback to ensure ongoing effectiveness.
Step 5: Incident closure
Establish closure through postmortem documentation and assessing response actions. This evaluation identifies opportunities for improvement, aiding the development proactive measures for future incidents and bolstering organizational resilience.
Rechecking the incident’s initial categorization is vital; misclassifications can increase MTTR.
Once the closure checklist is complete, share a detailed report to enhance trust with stakeholders. Automation can streamline closure using a set wait period post-resolution before auto-closing. If an incident recurs shortly after closure, you may need to reopen it. Logging a new incident is typically necessary if a longer duration elapses.
Incident management often requires a time and resource-intensive process with many stakeholders. Yes, it’s challenging, but AIOps helps simplify it.
7
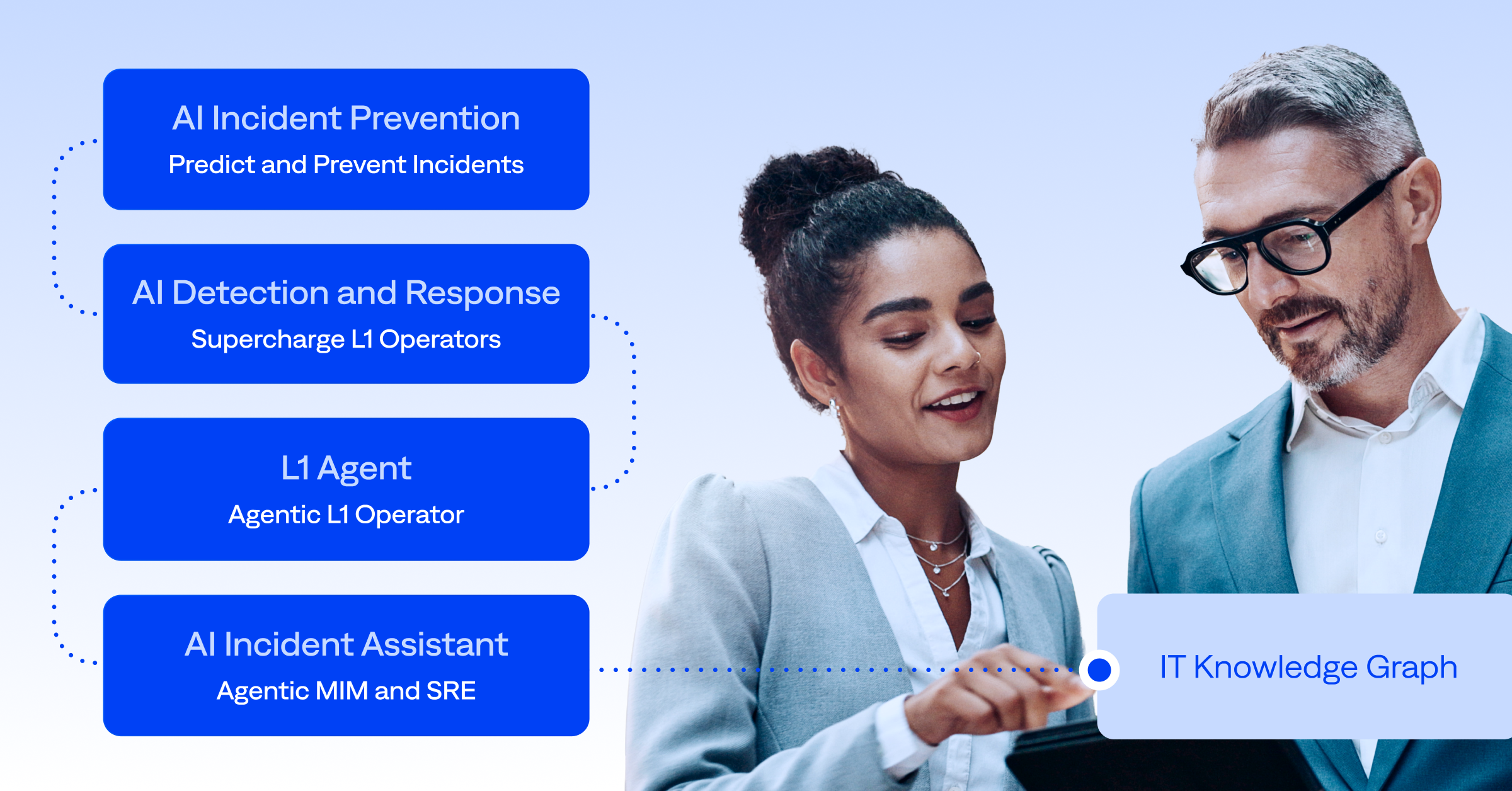
How to optimize IT incident management with AIOps
To remain productive and efficient, it’s important to focus on optimizing and using incident management best practices. Automate as much as possible to rapidly identify, assess, and resolve issues.
Clearly defining, optimizing, and using AI is critical for faster, smarter resolution — and to manage team workloads. AIOps optimizes traditional practices in a variety of ways.
Prioritize early detection with AI insights
Most IT teams have more than 20 observability and monitoring tools creating an overwhelming stream of alerts. BigPanda Alert Intelligence distills event data so teams can act quickly. Help your ITOps, NOC, and SRE teams recognize incidents faster. AI-powered workflow management tools and examining patterns from knowledge bases save valuable time with early detection and efficient presentation of incidents to IT staff.
Enhance categorization with machine learning
AIOps uses ML to categorize different incident types precisely. Use AI and ML to automatically correlate related alerts into high-level incidents using time, topology, context, and alert types. This not only accelerates the management process but also reduces human error.
You can reduce manual investigation by surfacing historical incident context to deliver more actionable insights. By analyzing historical data, AIOps can predict the nature of an incident, ensuring the right tools and knowledge are promptly accessed. BigPanda Similar Incidents turns legacy knowledge into actionable, AI-driven data to manage active incidents.
Streamline incident management with workflow automation
Automate notifications and updates for internal teams and customers. AI accelerates incident investigation and resolution by mobilizing the right teams and experts with automated notifications and ticketing. Workflow automation ensures that timely and consistent updates get to the right team at the right time.
Improve incident visibility with data and dashboards
AIOps aids in systematically handling and reviewing major incidents. Advanced analytics and dashboards provide deeper insights, highlighting recurring patterns and potential workarounds. This addresses immediate concerns and assists with visibility and devising proactive strategies. BigPanda Unified Analytics provides teams with a clear view of operations, allowing them to track KPIs and patterns to identify opportunities and support continuous optimization.
Automate root-cause analysis
Root-cause analysis is traditionally used after an outage to identify how to prevent future incidents, maintain an agile environment, improve processes, and eliminate known symptoms. BigPanda enables ITOps and DevOps teams to automate incident intelligence and fix issues at the source in real time to greatly reduce MTTR.
8
Automate incident management to speed resolution
BigPanda AIOps lets you harness the power of AI to detect incidents swiftly and categorize them accurately, streamlining responses and reducing human error. With our AIOps platform, gain high efficiency in automating crucial processes, from notifications to root cause analysis, ensuring timely resolutions and continuous improvement in your IT operations.
Enhance your visibility and insights with BigPanda advanced analytics and dashboards. Stop incidents from becoming outages by using AIOps for faster, more proactive incident management. Explore the BigPanda platform.