Intelligent alerts and alert management best practices
As an ITOps leader, you know managing enterprise IT can be challenging, with its mix of old and new, on-site and cloud-based systems. Closely monitoring each part of the system infrastructure and its many components is a constant struggle, forcing you and your team to juggle non-stop alerts and keep services up and running.
How can you stop alert fatigue and gain clarity when alerts are incessant, unclear, and lack the necessary context? The answer lies in intelligent alerts.
What is an intelligent alert in ITOps?
A standard IT alert is a notification of an issue in your IT environment. These alerts become ‘intelligent’ when they are enriched with valuable technical and business context and correlated together using AI and ML into an incident. This context typically includes:
- Configuration item (CI)
- Designated ownership
- Proper routing
- Alert business impact
- Dependencies, including impacted services and apps
- Runbooks and knowledge-base URLs
AI/ML enables your alert to be smart by adding context and sifting through minor alerts and focusing on significant issues. This enables IT professionals to proactively address problems before they affect the system’s users. Read on to learn more about:
- Why ITOps needs intelligent alerts
- The evolution of alerting systems
- The need for intelligent alerts
- Five best practices for implementing intelligent alerts
- How AIOps powers intelligent alerts
- How BigPanda AIOps helped Tivo achieve 94% alert noise reduction
- Unlock the power of Alert Intelligence with BigPanda
The evolution of alerting systems
Alerting systems in IT Operations have evolved significantly from manual monitoring days to complex, automated notifications. As IT environments expand and diversify, incorporating new technologies and monitoring tools, the original purpose of certain alert thresholds may become obsolete, or the creators of these thresholds may leave the organization.
This often leads to a decline in alert quality, with crucial alerts becoming difficult to distinguish amidst the noise. The continuous influx of alerts can inundate incident management processes without routine reviews to refine or refresh alerting rules, leading to overwhelmed systems and strategies.
The need for intelligent alerts
The modern ITOps landscape, characterized by its complexity and scale, necessitates a smarter alert approach. This stems from the four main challenges faced in alert management: volume, actionability and accuracy, timeliness, and context.
- Volume: With the explosion of data in today’s IT environments, teams are bombarded with more alerts than they can manage. Intelligent alerts help by sifting through the noise to spotlight the issues requiring attention.
- Actionability and accuracy: Intelligent alerts are designed to filter out false positives and benign events. They provide clarity on which alerts are actionable, letting you avoid the pitfalls of alert fatigue and the risk of overlooking critical issues.
- Timeliness: The speed with which ITOps teams detect and respond to incidents can be the difference between a minor hiccup and a costly outage. Intelligent alerts are timely, and their additional context gives first responders the necessary insights. This lets them rapidly resolve more incidents independently without escalating to L2/L3 resources.
- Context: Most importantly, intelligent alerts bring a wealth of context. Drawing connections between disparate data points such as change, topology, and business logic across various tools and teams provides a holistic view of the situation. This context empowers ITOps to make informed decisions quickly.
Best practices: Five steps for intelligent alert management
Implementing best practices for intelligent alerts is essential for streamlining response processes and elevating operational efficiency with targeted actionable notifications.
Step 1: Assess and manage alert quality
To reduce alert noise and continually improve the alerting environment, organizations need to categorize the “quality” of different alerts and differentiate those that are actionable and those that just generate noise. Organization-specific definitions for these quality levels can follow these general guidelines:
Step 2: Concentrate on your sphere of influence
Securing organizational commitment enhances the quality of alerts and incident response. Target an area with known technical and business dynamics but poor alert quality. This knowledge allows you to effectively enhance alerts by supplementing missing information. Demonstrate the benefits of these improvements in quality through targeted key performance indicators (KPIs), analytics, and dashboards.
Step 3: Prioritize alerts based on business impact
ITOps leaders should prioritize actions based on business consequences, not just technical metrics. For instance, issues in a main revenue-driving application should take precedence over lesser-used systems. To facilitate this prioritization, incorporate clear business context into alerts established by consensus across teams.
Step 4: Implement collaborative review for continual improvement
Effective alert and incident management involves constant evaluation to unify and refine response processes among diverse teams. Regularly assessing KPIs and business results with stakeholders from ITOps to DevOps ensures a shared understanding of achievements and areas for enhancement, fostering a sense of ownership and dedication to quality.
Step 5: Maintain alert system health
Regular maintenance of the alert system is crucial to ensure proper categorization, escalation, and resolution. This practice avoids skewed KPIs resulting from bulk resolutions of pending alerts. Consistent management provides a more accurate picture of the response team’s efficiency, facilitating the transparent tracking of progress toward business and technological goals.
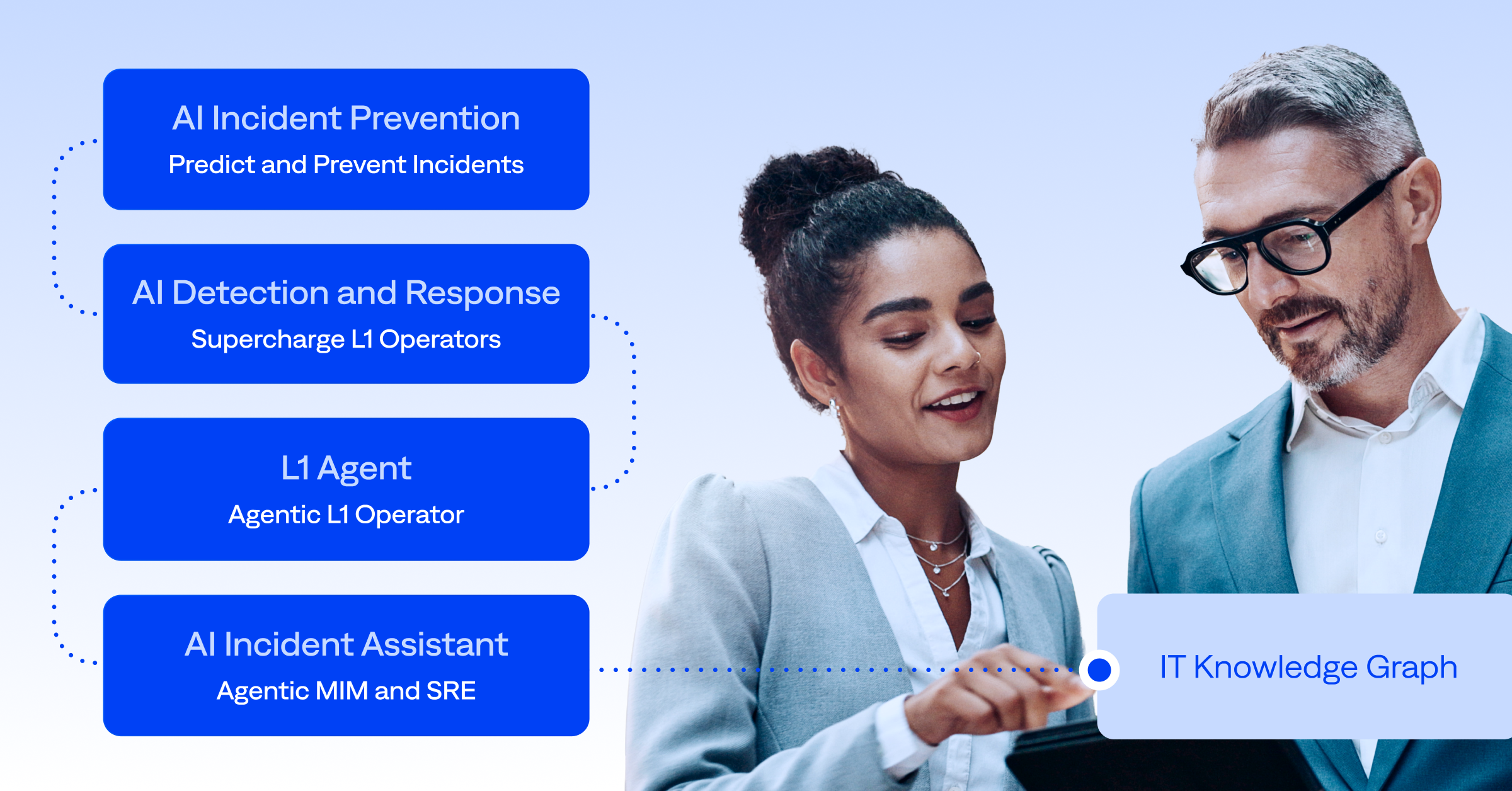
How AIOps powers intelligent alerts
Integrating AI into ITOps marked a shift for intelligent alerts prioritizing relevance and accuracy over sheer quantity. Using AI and ML, it became possible to generate intelligent alerts and refine these alerts by identifying patterns in data and suggesting correlation patterns.
One critical correlation in ITOps is event correlation, which uses AI/ML to automate the analysis of monitoring alerts from networks, hardware, and applications to detect incidents and issues, improving system performance and availability.
AI/ML can detect meaningful patterns amid streams of information and identify incidents and outages. It speeds up problem resolution, enhancing system stability and uptime. Critically, AI/ML enhances event correlation by continuously ‘learning’ and improving algorithms using data and user input.
Here are specific examples of how AI improves event management:
- Monitoring integrations: AIOps platforms integrate with various monitoring tools, allowing for a unified view of all alerts and enabling more effective cross-system correlations.
- Event normalization: These systems standardize event data, which makes it easier to manage and understand, paving the way for quicker response actions.
- Event deduplication: By identifying and merging duplicate events, AIOps ensures that each unique issue is only alerted once, cutting down on noise and reducing alert fatigue.
- Event filtering: Non-essential alerts are filtered out, ensuring the focus remains on high-priority events requiring immediate attention.
- Event enrichment: Contextual information is added to alerts, providing a deeper understanding of the underlying issues and facilitating more informed decision-making.
- Event aggregation: Related alerts are grouped, offering a cohesive picture of widespread issues or systemic problems, which can lead to more strategic and long-term solutions.
Jumpstart your intelligent alert journey with BigPanda
By harnessing the power of AIOps and intelligent alerting, teams can cut through the noise to focus on the incidents that truly matter, enhancing both efficiency and system reliability. Take the first step towards transforming your ITOps alerting system by exploring the capabilities of BigPanda’s Unified Analytics. Key out-of-the-box capabilities to help you identify where and how to improve alert quality include:
- Monitoring event dashboard: This dashboard gives a high-level overview of how BigPanda interacts with your monitoring tools, including event volumes per monitoring source and hour. Gain a single pane of glass view into all the events your monitoring tools are creating and tracking so it’s easy to identify trends and areas for change.
- Alert quality dashboard: Go deeper into compressed alerts with BigPanda. Gain more context into your alert noise with the Alert Analysis Dashboard. Explore your alerts and answer questions including “Which hosts or applications create the most alerts/noise?” or “Which alerts have been the most common in a certain timeframe?” It can also show the quality of alerts and incidents, how they have been enriched, and the impact of actionable alerts on MTTR.
Experience firsthand how BigPanda can revolutionize your alert management with a personalized platform demo today—because when every second counts, intelligent alerts make all the difference.