Splunk integration with BigPanda
Correlate machine data from Splunk with alerts from other monitoring tools, so that you can detect, investigate and resolve incidents quickly.
Many enterprises have invested in Splunk deployments which allow them to search, monitor and analyze machine data generated by their infrastructure. One key feature Splunk supports is Saved Search Alerts, which allows Splunk users to fire alerts based on Splunk search data.
Depending on Saved Search configurations, these alerts can quickly pile up. To deal with this, many IT Ops teams endlessly tweak thresholds and suppress alerts to reduce noise and catch disruptions, problems and outages on time, but this can cause the opposite problem: missing a crucial alert that could have prevented or shortened an incident.
When IT Ops teams can’t get effective Splunk alerts (generated at thresholds that are right for their environment) and correlate them against alerts collected from all the other monitoring tools in the environment, these teams can’t detect incidents as they happen, and are forced to deal with them only after they have escalated into an outage.
For application owners (DevOps teams today), this means that their applications are subject to longer periods of downtime or degraded application performance and availability.
For IT execs and BU/LOB/Service owners, this means that incidents take longer to resolve (higher MTTR). In turn, that increases the cost of downtime and the impact to critical revenue-generating applications and services.
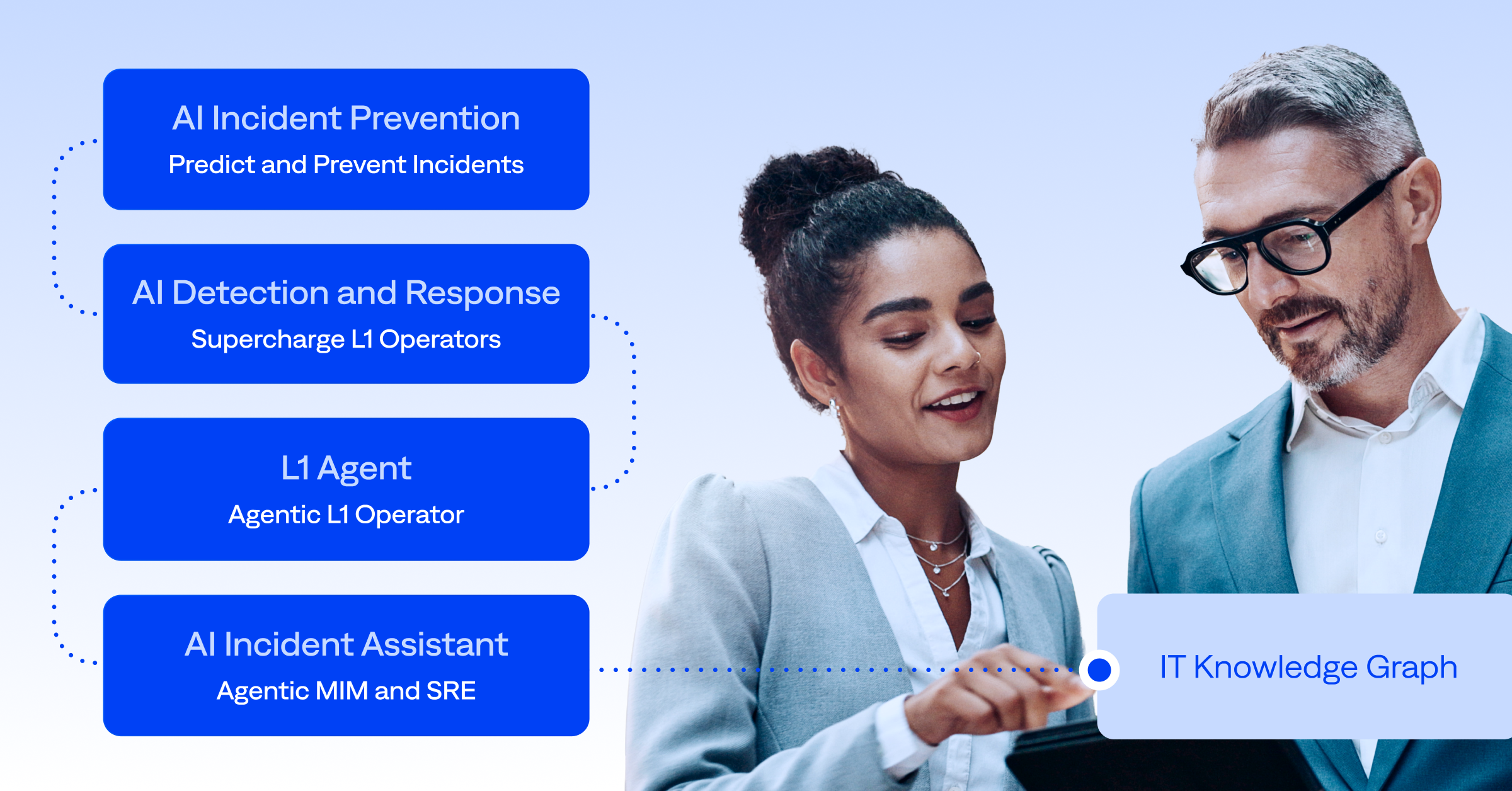
BigPanda gives Splunk users a holistic view
BigPanda’s integration with Splunk allows customers to correlate alerts from Splunk, and alerts collected from other monitoring tools, into high-level incidents in BigPanda. These correlated alerts can be enriched with contextual data from other tools. All of this is managed using a dedicated dashboard unique to the integration.
Here is how BigPanda handles the lifecycle of Splunk alerts
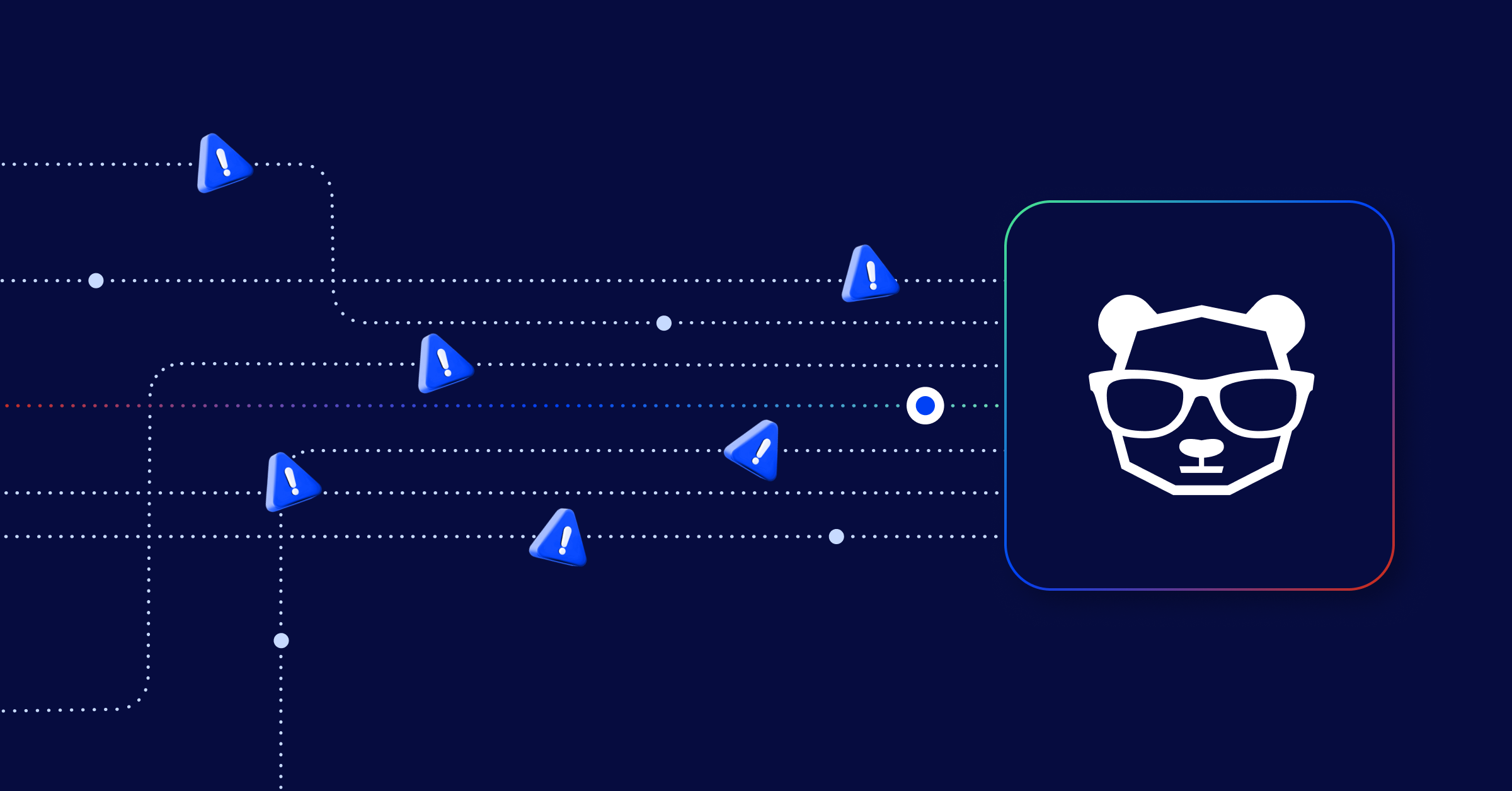
Correlation
Bring data from multiple sources into a single incident
The integration allows users to create BigPanda incidents based on Splunk Saved Search alerts that have been correlated with other alerts BigPanda has received. It works by using the Custom Alert Actions capability in Splunk to add an action specifically to send the alert into BigPanda.
BigPanda then correlates these alerts with events received from other tools. These correlated incidents commonly include monitoring data collected from a broader set of monitoring tools—such as application monitoring, system monitoring, network monitoring and other tools—because incidents in today’s complex IT stacks are detected by several different tools at the same time. By correlating all related alerts together, BigPanda prevents IT Operations teams from wasting time investigating tens of related alerts for the same incident or outage.
Enrichment
Add context from topology and change tools
Further, during the process of ingesting alerts from Splunk and other monitoring tools, BigPanda enriches them with contextual and meta data collected from CMDB, change and topology tools. This helps IT Ops, NOC, DevOps and SRE teams detect incidents faster, understand the root cause, the impact of these incidents and how best to share or route them for rapid investigation and resolution. The integration can also automatically close incidents in BigPanda whenever Splunk alerts expire.
Management
Easily configure and normalize alerts
Finally, BigPanda provides simple and efficient management of all alerts coming from Splunk through a dedicated alert management dashboard. A native Splunk app lets you easily configure Splunk alerts to be sent to BigPanda. The integration then automatically normalizes the alerts into one or more BigPanda alerts.
For more information, please check out the Splunk integration information in the BigPanda documentation center.